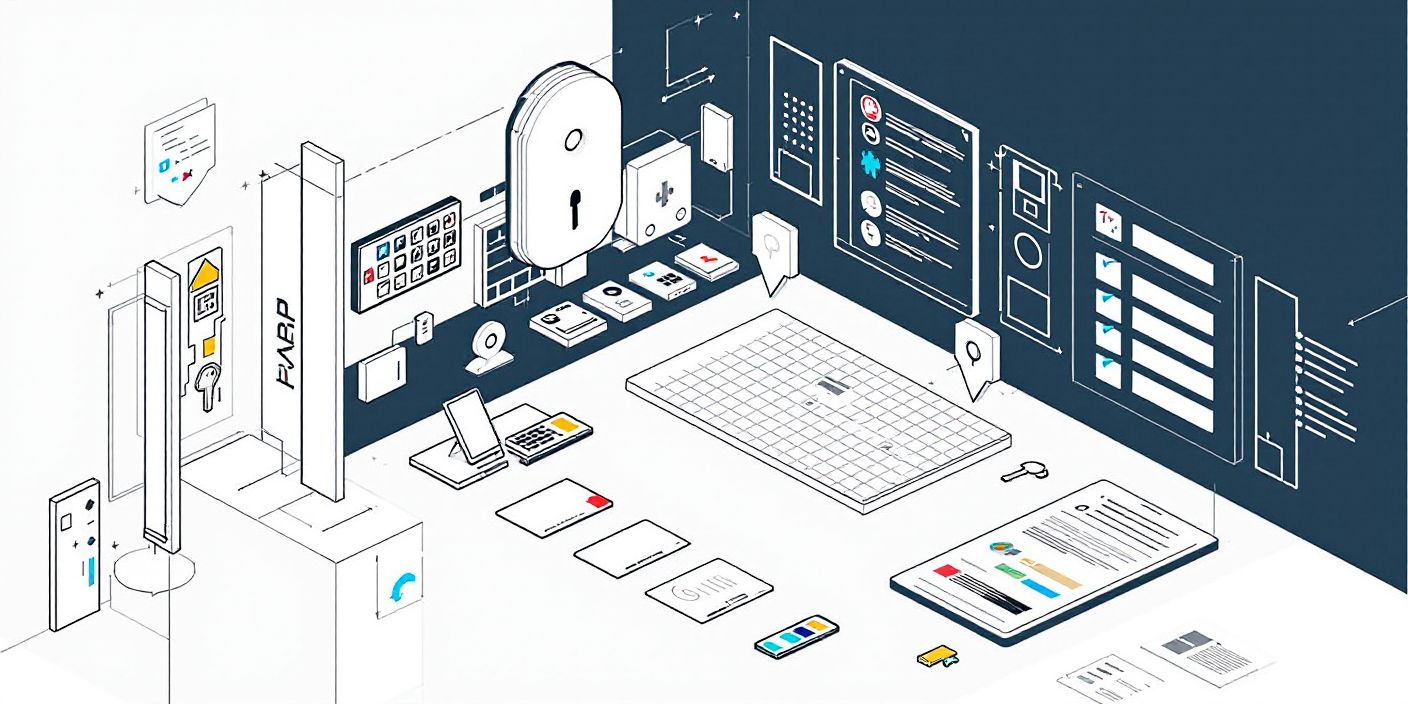
The Key Management System helps organizations maintain strict control over physical keys, ensuring accountability, security, and operational efficiency. It eliminates manual tracking and enhances the overall security infrastructure.

About Key Room Management
The Key Management System (KMS) within iFaziG is designed to streamline the handling, tracking, and security of physical keys across an organization. It provides a centralized platform for managing the lifecycle of keys, from issuance and tracking to return and maintenance. This system ensures that keys are always accounted for, reducing the risk of loss, theft, or unauthorized access, and ensures compliance with security protocols.
Awesome Features
01Centralized Key Register
All keys are digitally recorded in a centralized register, including key numbers, associated departments, locations, users, and status. This register ensures easy tracking, accountability, and efficient key management throughout the organization.
02 Key Issuance and Tracking
Keys are issued through the system, with each transaction recorded to maintain a complete history. This feature allows administrators to track who holds which key, for what purpose, and for how long. Alerts and reminders can be set for the return of keys, ensuring that no key is overlooked.
03 Access Control and Security
The system integrates with access control systems to ensure that only authorized personnel can access certain areas. By associating key access with user credentials, KMS enhances security and ensures that keys are only available to those with appropriate clearance.
04 Audit Trail and History
A detailed audit trail is maintained, documenting all key transactions including check-ins, check-outs, returns, and any changes to the status of keys. This audit trail is vital for security reviews, operational transparency, and compliance with internal and external regulations.
05Key Maintenance and Replacement
The system tracks key wear and tear, ensuring timely maintenance or replacement when necessary. It also manages key duplication requests, ensuring that the right protocols are followed when additional copies are required.
06Duplicate Key Process (Request and Issue with Approval)
Requests for duplicate keys are handled through a
structured approval process
Request: Users initiate a request for duplicate keys through the system, providing
justification for the need for additional copies.
Approval: The request is sent to the designated approver (e.g., Facility Manager or
Security Head) for review. The approver can approve or reject the request based on
organizational policies.
Issuance: Once approved, the duplicate keys are issued, and the transaction is
logged in the system. The issuance is tracked with the same level of scrutiny as the
original key issuance, ensuring that all duplicates are fully accounted for.
How it works
Register
Keys
Keys are added into the system with detailed information such as department, location, and assigned user.
Issue and
Track Keys
Keys are issued to authorized personnel, and their usage is tracked in real time, ensuring that all keys are accounted for.
Monitor and
Secure Access
The system integrates with access control measures, ensuring that only authorized users can access specific areas or keys.
Request and Approve
Duplicate Keys
Users can request duplicate keys, and the request is sent for approval. Once approved, the duplicates are issued and tracked in the system.